Corporate Governance
Information Security
As the Group, trust-based relationships with stakeholders are an essential part of our business growth. For this reason, we are striving to strengthen information security as a high priority by setting "Protect consumers and provide them with an environment where they can safely enjoy the company's content" as one of the Group's material issues. The Group will continue to provide an environment where customers can safely enjoy our services by building a robust Group-wide security framework and ceaselessly working to protect personal information.
Information Security Basic Policy
Our Group places great importance on being a trusted company among our stakeholders, including customers and business partners, while creating new value through digital entertainment and contributing to societal development. We are committed to complying with applicable laws, regulations, and contractual requirements, as well as to appropriately managing information assets and data. Through these efforts, we are committed to providing safe and secure services while continuously improving our information security management system.
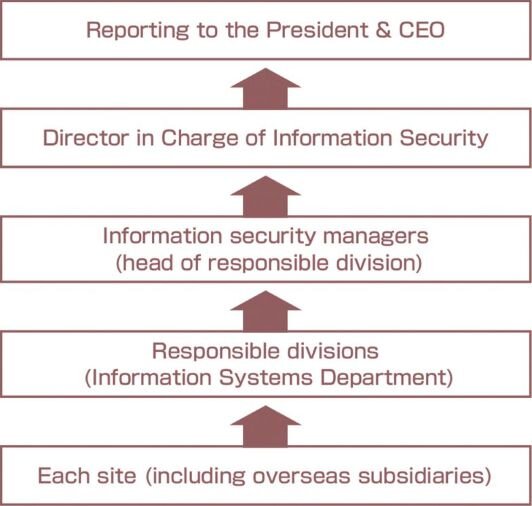
Governance Structure
The Group has established an escalation process for cases where it acquires risk-related information. In the event of an incident, a response system will be established under the direction of the director in charge of information security, and when required, the Risk Management Committee, chaired by the President and CEO, will be convened.
Moreover, we have created a Personal Data Handling Manual for each division and have established a system whereby, in the event of a privacy-related incident, the person in charge of handling personal data in each division promptly reports the incident to relevant parties, including
responsible managers in related divisions. Additionally, reports are made to the President and CEO as appropriate.
Director in Charge of Information Security
The Group has designated the officer in charge of information systems as the Director in Charge of Information Security. Currently, the Deputy General Manager of the Business Administration Division serves as the officer in charge of information security for the Group.
Escalation System
Risks
The Group considers the following to be business risks related to information security:
● System outages, or data leaks, loss, or tampering due to unauthorized access or cyberattacks
● Information leaks due to the removal of important information
● Increased costs and procedures associated with compliance with relevant laws and regulations
● Liability for lawsuits, fines, or damages arising from information security incidents
● Decline in social trust due to information security incidents
Strategies
Risk Control
a. Unauthorized access and malware countermeasures
We implement integrated and effective measures that incorporate a multi-layered defense against unauthorized access and other risks, while also preparing for external attacks. We have also added multi-factor authentication (MFA) for access to information systems and cloud service, combining multiple types of authentications to reduce the risk of unauthorized access. We constantly collect information on new standards and trends and update our security management information to ensure that we can implement optimal countermeasures, while assessing the need for them.
b. Information leak risk countermeasures
To reduce the risk of information leaks, we encrypt files containing personal or confidential information using information protection tools. We have also taken measures to protect content so that, even in the event of a data leak, nobody but relevant personnel can access the contents. In addition to strengthening the management of information taken outside the company by employees, we also collect operation logs to help prevent information leaks from within the organization.
c. Natural disaster risk countermeasures
To increase business continuity, we promote the use of cloud platform environments in compliance with international standards to prevent the shutdown of mission-critical systems due to major earthquakes and other natural disasters, along with cyber-attacks. We are also strengthening backup networks between each base within the Group, as well as eliminating single points of failure and adding redundancy to each base's network, thereby reinforcing backup networks.
Employee Education
We regularly conduct information security training and targeted attack email drills to enhance employee awareness and skills. Specifically, we provide information security training via e-learning for all employees including those at domestic and overseas Group subsidiaries and have achieved a 100% completion rate. The Group also implements targeted attack email drills, sending simulated attack emails to employees to teach them the appropriate response, thereby enhancing their awareness and ability to respond to attacks. As a result of training, the Group demonstrated a higher level of responsiveness than the average across domestic Japanese companies for both email opening rate and reporting rate. Furthermore, improvements could be seen in FY2024 compared to FY2023, confirming the continual effectiveness of training.
Management of domestic and overseas Group subsidiaries
By centralizing management of Group-wide internal information infrastructure within the Information Systems Department and clarifying responsibilities and standardizing operations, the Group has strengthened our management framework and improved operational efficiency. Furthermore, by centralizing the management of the Company's internal information infrastructure, the Group has established a unified security operation framework that enables prompt responses to potential threats and reduces the risk of information leaks, thereby ensuring the security of information assets across the entire Group. Through these initiatives, the Group strives to maintain stable operations and a high level of security.
Establishment of Action Plan (BCP Measures)
The Group has established an action plan that outlines specific procedures for detection, initial response, triage, and resolution for each type of information security incident, in order to ensure preparedness for emergencies. As a result, the Group has established a system that enables a swift and appropriate response even in emergencies. In the event of an incident, related divisions will work together to respond to the incident in accordance with the escalation process outlined in the Group's governance structure.
▶ BCP measures
As part of our BCP measures, the BCP Basic Global Regulations stipulate that incidents impacting business continuity beyond the scope of "risk incidents" defined in the Risk Management Global Regulations be classified as "business crisis incidents." In such cases, we will establish a Business Crisis Response Headquarters. In respect of the headquarters, the rules grant it temporary authority beyond that granted by regulations during normal times and enable it to omit or simplify certain internal procedures.


